Wireless Network
Penetration Testing
Wireless signals don't respect walls
neither do cybercriminals.
Wireless Network Penetration Testing is a targeted evaluation aimed at identifying and exploiting vulnerabilities in wireless networks, including Wi-Fi networks and other wireless communication standards. Some of these vulnerabilities surface due to :
Weak Encryption & Authentication (WEP, WPA2 and WPA3 flaws, weak passphrases)
Evil Twin & Rogue AP Attacks (unauthorised access points)
MAC Spoofing & Deauthentication Attacks (disconnecting users to capture credentials)
Man-in-the-Middle (MitM) Attacks (eavesdropping on network traffic)
WPS PIN Vulnerabilities (brute-force attacks on WPS-enabled devices)
Lack of Network Segmentation (cross-network lateral movement)
Poor Logging & Monitoring (lack of intrusion detection for Wi-Fi threats)
Corporate wireless rollouts
Wireless signals don't respect walls
neither do cybercriminals.
Wireless Network Penetration Testing is a targeted evaluation aimed at identifying and exploiting vulnerabilities in wireless networks, including Wi-Fi networks and other wireless communication standards. Some of these vulnerabilities surface due to :
Weak Encryption & Authentication (WEP, WPA2 and WPA3 flaws, weak passphrases)
Evil Twin & Rogue AP Attacks (unauthorised access points)
MAC Spoofing & Deauthentication Attacks (disconnecting users to capture credentials)
Man-in-the-Middle (MitM) Attacks (eavesdropping on network traffic)
Corporate wireless rollouts
Poor Logging & Monitoring (lack of intrusion detection for Wi-Fi threats)
Lack of Network Segmentation (cross-network lateral movement)
WPS PIN Vulnerabilities (brute-force attacks on WPS-enabled devices)
Powered by Proven Methodologies
This service simulates real-world attacks to test the effectiveness of security measures, uncover weaknesses in encryption, authentication, and connection protocols and assess the potential for unauthorized access or data interception. Our Wireless Network Security Testing is based on standards like IEEE 802.11, NIST, and CIS Benchmarks.
Our assessment evaluates whether an attacker can:
Intercept Wireless traffic
Intercept wireless traffic and extract credentials.
Gain Authorised Access
Gain unauthorised access to corporate or guest Wi-Fi networks.
Denial-of-Service (DoS)
Perform Denial-of-Service (DoS) attacks on wireless infrastructure.
Compromise Wireless Clients
Compromise wireless clients via phishing or rogue AP attacks.
Actionable Recommendations You Can Bring To Stakeholders
We deliver comprehensive, cryptographically signed penetration testing reports that are both verifiable and tamper-proof. Each report includes detailed vulnerability backgrounds, clear impact assessments, and actionable recommendations. And because security is a global concern, our reports are available in 113 languages—ensuring your cross-border teams are always in the know.
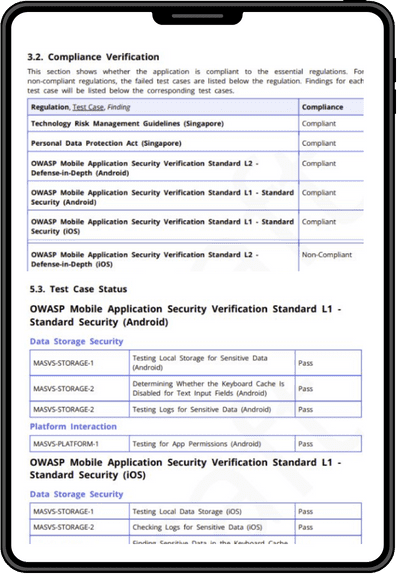
Compliance Verification Reporting
The report clearly shows the specific standards the app complies to.
Detailed down to the Test Cases
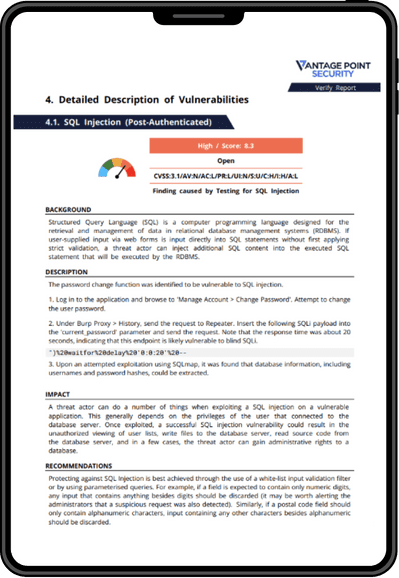
Detailed Background
We explain the vulnerability clear enough for technical and non technical stakeholders to understand.
Impact statements
Explaining the business impact of the vulnerability.
Recommendations
Actionable insights stakeholders can take to remediate gaps.
SPEAK TO AN EXPERT
Know Your Vulnerabilities.
Start Securing your Assets Today.
Experts in Penetration Testing
innovation and IP development
Red Team Providers in Southeast Asia
80,000+ hours of yearly pentesting
Specialists in AppSec
Quality Assurance with Velocity
Other CREST Approved Penetration Testing Services
Web Application
We secure your web applications by identifying injection flaws, authentication bypasses, and business logic vulnerabilities that could expose your systems, ensuring compliance to technical and regulatory standards.
Mobile Application
We secure your iOS and Android applications by identifying code vulnerabilities, insecure data storage, and authentication flaws, ensuring compliance to standards like the OWASP MASVS and more.
Network
We secure your network infrastructure by identifying misconfigurations, weak protocols, and access control flaws across routers, switches, servers, and endpoints. We ensure compliance to many industry standards.
API
We secure your APIs against data breaches and unauthorized access by identifying authentication flaws, injection vulnerabilities, and more in your API endpoints, ensuring compliance to standards like OWASP Top 10 and more.
Thick Client
We secure your desktop applications through thorough testing that identifies local storage vulnerabilities, communication protocol weaknesses, and authentication flaws that could compromise user data.
Active Directory
We secure your Active Directory infrastructure through specialized testing that identifies privilege escalation paths, credential vulnerabilities, and configuration weaknesses that could lead to domain compromise.
Other CREST Approved Penetration Testing Services
Mobile Application
We secure your iOS and Android applications by identifying code vulnerabilities, insecure data storage, and authentication flaws, ensuring compliance to standards like the OWASP MASVS and more.
Web Application
We secure your web applications by identifying injection flaws, authentication bypasses, and business logic vulnerabilities that could expose your systems, ensuring compliance to technical and regulatory standards.
Network
We secure your network infrastructure by identifying misconfigurations, weak protocols, and access control flaws across routers, switches, servers, and endpoints. We ensure compliance to many industry standards.
API
We secure your APIs against data breaches and unauthorized access by identifying authentication flaws, injection vulnerabilities, and more in your API endpoints, ensuring compliance to standards like OWASP Top 10 and more.
Thick Client
We secure your desktop applications through thorough testing that identifies local storage vulnerabilities, communication protocol weaknesses, and authentication flaws that could compromise user data.
Active Directory
We secure your Active Directory infrastructure through specialized testing that identifies privilege escalation paths, credential vulnerabilities, and configuration weaknesses that could lead to domain compromise.